Beginner’s Guide to Crypto Security: How to Protect Your Crypto from Intruders

Cryptocurrency has attracted many scammers and hackers. Here's how to protect your crypto by employing these crypto security standards.
How secure is cryptocurrency?
The DeFi hype has resulted in more crypto hacking and fraudulent activities. People became more willing to use less secure systems because they were afraid of missing out (FOMO).
Since 2020, cryptocurrency theft has increased by 516%, totaling $3.2 billion in cryptocurrency, 72% of which is stolen cash via DeFi protocols. Fraud caused the loss of more than $7.8 billion worth of cryptocurrencies, which is a huge increase of 82%. Most of this money was made through "rug pull" schemes, a crypto scam that is fairly new but very popular.
Vulnerabilities in Cryptocurrency Infrastructures
When a lot of cryptocurrency assets are stored on an exchange, it can draw the attention of malicious people. If your account is hacked or you fall for a scam, it's hard to get back all of the cryptocurrency that was stolen. Therefore, users are not entirely protected from losing their own investments.
Even though outside exchanges are often to blame for security problems with cryptocurrencies, sometimes the infrastructure is also to blame. There are several holes and flaws in the infrastructure of cryptocurrencies that hackers and scammers use to trick crypto traders and investors who don't know what's going on:
I. Listing Identical Crypto Name
Listing the same token names on a decentralized exchange is a slightly more complicated way to steal cryptocurrency. For example, scammers can make an ETH+ token to trick people who don't know much about trading cryptocurrencies.
II. "Social Engineering Methods"
- Using Deep Fakes
With deep fake technology, scammers can pose as crypto celebrities on Telegram channels and YouTube videos. With the celebrity's fame, scammers can get crypto traders and investors to tell them their secret phrases, which gives them access to their accounts from any device.
- Phishing Sites
In many cases, developers will set up a phishing site and send out viruses that change the recipient's address when sending a transaction. The scheme starts with an email containing a link connected to the phishing site that looks exactly like the original.
- Cyber Security Cryptocurrency Scams
In this classic scam, a user's wallet or exchange sends them a message saying they need to finish a transaction, log in to their account, or install a new program to keep their cryptocurrency wallet safe.
III. Using Malware/Virus
Fraudsters sometimes use malware to change the wallet address of the recipient right before a user sends crypto to that person. During a transaction, the user types in the address of the recipient, but malware changes it to the address of the scammer's wallet. The coins will end up in the hands of scammers if the sender does not check the recipient's address before sending them.
In other cases, investors receive an email or a private message containing a link. Once the button is clicked, a piece of malware called a "keylogger" will be put on the computer. This malware can record passwords, clipboard history, and other credentials.
Crypto Security Mistakes You Should Avoid
1. Participating in Rug Pulls
The crypto rug pull scan is pretty simple. Developers produce a bogus token that is then swapped for valuable crypto. Most rug pulls are accompanied by a lot of marketing and hype to get money from investors. Then, token creators will disappear once they've collected a significant amount of valuable crypto.
A cryptocurrency rug pull is easy to spot because it raises so many red flags:
- A Suspicious Amount of Liquidity
- Liquidity at Developers’ Disposal
- Mooning of Price Within Hours
- The influx of Influencers and Promotions
- The White Paper Sounds Like a Sales Page
- Malicious or Copy-Pasted Codes
- Look Out for Whales
Read more about crypto rug pulls: Tips to Avoid Being Involved in a Rug Pull in 2022
2. Bragging on Social Media
No one has to know how much crypto you have. Just because crypto is a digital currency doesn’t mean malicious individuals won’t try other ways to rub you. “Brute force” can be used to extract your private keys. Someone can also attack and force you to transfer your crypto holdings at gunpoint.
3. Storing Private Keys Online
Cloud providers have their own servers that give you an interface to interact with your data. So, their server can be shut down, and you won't be able to get to your private keys. When they get hacked, you get hacked as well. A single successful attack could also take down millions of records in one go, including your precious data.
Pro Tip: Write down your private keys and seed phrases in a notebook, then keep that notebook inside a safe or a secure location.
4. Talking to Strangers on Social Media
Cybercriminals prey on unsuspecting traders who appear to be crypto-illiterate. Fake admins of Telegram or Discord groups will message you personally and represent themselves as one of the group's administrators. They will request your private keys or seed phrase after establishing your trust. In certain circumstances, fraudulent administrators will invite you to use a platform so that they can harvest confidential information.
Pro Tip: If someone you don't know messages you about cryptocurrency, block them right away—No-Questions-Asked!
5. Ignoring a Multi-Layered Security Feature
With too many cyber threats in the cryptoverse, financial platforms should employ many layers of security. Layered security provides a comprehensive approach to cyber defense rather than merely waiting for assaults to strike from end to end. A multi-layered security feature considers the diversity of channels each malware could be injected into. Therefore, it considers the relevance of network and end-user-level security.
In other words, always use 2-Factor Authentication and other additional layers of crypto security available on the exchange.
Crypto Security Guide and Tips
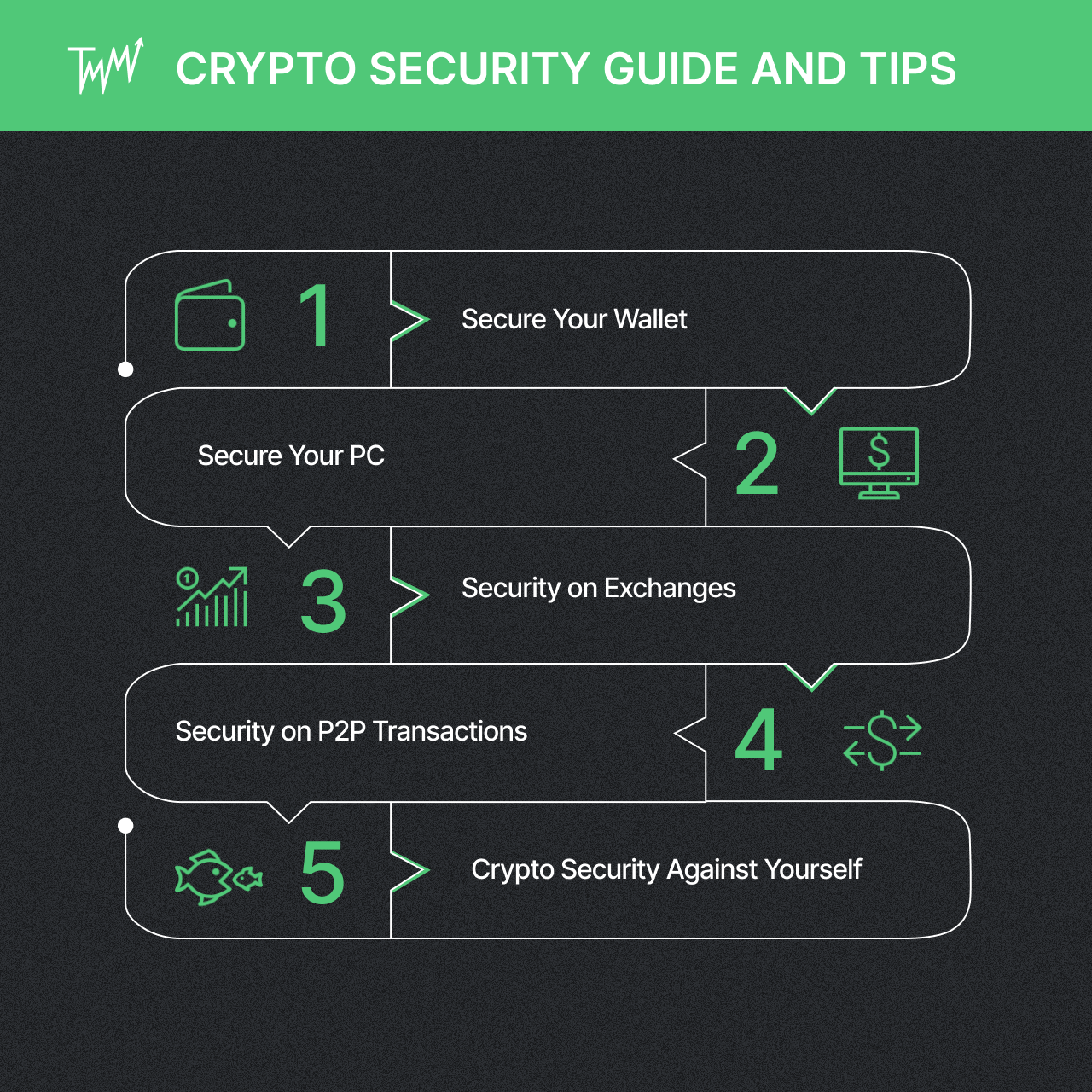
Crypto Security for Your Wallet
Beginners tend to retain their coins on the exchange they got them from, thus trusting the exchange to keep the coins secure, giving up control over their crypto. This is called a "Custodial Wallet," and it is prone to cryptocurrency wallet security breaches.
A Non-custodial wallet is the best place to keep your cryptocurrencies after withdrawing them from an exchange. It is possible to have a wallet installed on a mobile phone or a desktop computer. However, a hardware wallet is the most secure cryptocurrency wallet. Usually, each cryptocurrency requires a dedicated wallet, although most wallets can handle a variety of coins.
Crypto Security on Your PC
Hackers frequently target easy targets. Many hackers don't go after specific individuals. Instead, they build massive networks of compromised PCs. So, your current computers and networks shouldn't have any computer viruses that could be used to track keystrokes, credentials, or download other malware.
Pro Tip: Don't use the same password for your critical accounts, such as your bank accounts, crypto trading accounts, and Wi-Fi credentials.
Malware signatures should be added to anti-virus programs like ZoneAlarm, Malwarebytes, and AVG. Do a complete scan of all your machines regularly. Also, consider installing a browser plugin that blocks zero-day malware and phishing websites.
Crypto Security on Exchanges
Centralized exchanges are far more vulnerable to hacking and data breaches. For hackers to gain access to users' holdings, financial information, and other potentially damaging data, they just need to get past the security measures of the exchange operator.
In contrast, a decentralized exchange is hard to hijack. Hackers would have to compromise every single user. The system's peer-to-peer approach allows little or no possibility for infiltration or manipulation. On the other hand, developers can easily list shitcoins on a decentralized exchange, which makes it easier to pull off a rug pull scam.
Pro Tip: Distribute your points of failure by opening accounts on reputable crypto exchanges. By doing so, you can avoid being paralyzed if a crypto exchange goes down or gets attacked.
Crypto Security on P2P Transactions
Peer-to-Peer transactions are plagued by a variety of vulnerabilities. The anonymity and decentralization of P2P transactions are the primary causes of most problems. P2P networks are vulnerable to many security risks, such as malware that changes your address, software that takes over your clipboard, and P2P scams.
While computer hygiene can easily solve software-related problems, P2P scammers can sometimes be too cunning. Fortunately, several crypto exchanges have security safeguards in place for their P2P transactions, such as Binance, Bybit, and Gemini. So, it's much more secure to limit your business to reputable exchanges rather than find someone from social media groups.
Still, your crypto security for P2P transactions is in your hands. Therefore, you should avoid transferring or demanding money from anyone you don't know or trust.
Crypto Security Against Yourself
It's common for beginners to succumb to FOMO (Fear of Missing Out) and FUD (Fear, Uncertainty, and Doubt). Always keep your emotions in check while beginning your crypto trading career. Here are some tips on how you can do that:
- Fundamental and Technical Analysis
In developing a trading strategy for cryptocurrencies, a trader should not just rely on technical analysis to make money. You'll also need to familiarize yourself with the tokenomics, utilities, and other macro-indicators of the project, as well as the founders and the team that put it together. Remember that each cryptocurrency requires a special blend of fundamental and technical analysis.
Read more about Fundamental Analysis in this article: Step-by-Step Guide: How to Get Into Crypto Trading – CORRECTLY
Read more about Technical Analysis: 7 Best Indicators for Crypto Trading
2. Risk Management
- Proportioning Position Size
Properly proportioning your position size is a key element of risk management. You could make too many large trades for your account if you don't know how to properly proportion your positions. Therefore, you'll become vulnerable when the market moves even just a few points against you.
Read more about proportioning position size: Bear Market Trading Strategy: How to Save Capital and Profit in the Bear Market
- Stop Loss & Take Profit
- Stop Loss is an execution order that terminates an open position when the price falls below a predetermined level. Stop Losses protect you from losing money on unsuccessful trades.
- Take Profit is a programmable order that closes open positions when prices hit a specified threshold. Take Profit allows you to exit a transaction before the market moves against you.
- Risk/Reward Ratio
The risk/reward ratio measures how much risk there is in proportion to the possible payoff. The more risky a trade is, the more lucrative it might be. To determine when to join and exit a transaction, you must understand the risk/reward ratio. You can compute the risk/reward ratio by using this formula:
Risk/Reward Ratio = (Target Price – Entry Price) / (Entry Price – Stop Loss)
Read more about Risk Management: Risk Management or How to Trade in the Red and Earn Money
3. Using a Crypto Trading Journal
When you keep a crypto trading journal, also known as a trading diary, you document all of your trades and any ideas or emotions that influenced your actions. Trading crypto becomes a game of chance if you don't utilize crypto charting tools, crypto technical analysis, or at least a free version of a crypto trading journal.
Read more about using a crypto trading journal: Crypto Trading Journal Review: CMM vs. TMM
Conclusion
Cryptocurrency has grown in popularity, and with it, many unscrupulous actors seek to exploit security issues of crypto infrastructure and human vulnerabilities.
It's a dangerous world out there. A ton of due diligence is required. By adhering to tight cyber security cryptocurrency standards, you can have secure cryptocurrency holdings in your wallet, protect yourself against scammers, and avoid losses.
